Is there any truth behind the alleged data breach at Fortnite maker Epic Games? Who launched the ransomware attack that caused a fallout at pharmacies? And what’s the latest on the heart-breaking hack of Finnish therapy clinic Vastaamo?
All this and much much more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by Jessica Barker.
Warning: This podcast may contain nuts, adult themes, and rude language.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Now, can we trust them? No! You'd have to ask that question!
Everything that comes out of their mouth is just verbal blah blah.
Smashing Security, Episode 362. Ransomware Fraud, Pharmacy Chaos, and Suicide with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security, episode 362. My name is Graham Cluley. And I'm Carole Theriault. And, Carole, this week we're joined by a special guest someone who's been on the show plenty of times before, but it is the newly anointed Dame Jessica Barker. Hello, Jess.
Hello, hello. Not quite a dame, actually.
Not a pantomime dame, either.
Not quite a dame. Stretching it a little bit there, but... But, you know, I'm not complaining.
So you've just been awarded an MBE for services to cyber security. Is that right?
That's correct. Yes. Feels very surreal. Popped to Windsor Castle. Had a little visit. A couple of dudes. Oh, right. A little visit with Prince William. And he asked me some pretty good questions about cyber security when he pinned the medal on me.
Are we confident he's got a good password and he's turned on two-factor authentication? Did you have a chance to just check his password?
You know, I didn't ask what his password was, but he assured me he's not going to be giving any money away to princes who promise him their fortune if he just transfers a little bit of money first. So I think we're all right. I think we're doing all right.
I guess the difference is that he does occasionally get genuine emails from foreign princes, whereas the rest of us can't believe them. So he's in a trickier position, you know, how can he tell?
Before we kick off, let's thank this week's wonderful sponsors, Collide, Kiteworks and Vanta. It's their support that helps us give you this show for free. Now, coming up on today's show, Graham, what do you got?
I'm going to be asking the essential question, who's frauding who?
Ooh, and what about you, Jess?
I'm talking more ransomware.
And I'm going to talk about when psychotherapy is not exactly what you expected. All this and much more coming up on this episode of Smashing Security.
Now chums, chums I think I'm speaking for all of us when I say that we all love video games don't we? We can't resist can we? There we are we're noshing away on our popcorn we're... I don't play... Do you play video games Jess? Do you play video games out there in Vegas?
I love Tetris. You know, that's my speed as well, actually.
Yeah, 35 years ago, that was a big deal. Well done. Right, okay. So you're up to speed.
It hasn't aged. It hasn't dated, I promise you.
I play Snake on my Nokia. A bit of Minecraft, you know.
Occasional Minecraft, I must admit. All right, okay. Well, at the end of February, headlines broke that Epic Games, do you remember Epic Games? They used to be called Epic Mega Games in my day, but now they're just called Epic Games. They are the people behind Fortnite, that incredible phenomena that I've never played or seen. Oh all the stuff you just don't want out there right? All the stuff.
And Fortnite is a phenomena it's so big it's it's where now movies are actually premiered on Fortnite you have rock stars performing at virtual events within the Fortnite game there's this huge... oh it's extraordinary it's a amazing amount of money that the Fortnite guys are making. So they have online stores.
So, so, so what? So you'd go to an online store and then you'd see a pre-ad, which would be a music video? No, no, no. I don't understand. You are in the virtual Fortnite world and there's a concert going on in the world where you can be doing all your Fortnite dancing and everything in front of the stage. And there up on the stage are the stars or the movie or... And lucrative, depending on what side you're on.
And potentially, yeah. Yeah, potentially very lucrative for the bad guys. And in this particular case, the people who claim to be behind their attack were a cyber crime group called Mogilevich. Have you heard of Mogilevich?
No.
No. Well, Mogilevich, it turns out, is a real person. There is a chap. I think he's called Semion Mogilevich or something. And he is on the FBI's, I think he's number 149 in their top most wanted.
You want to be, you know, I wonder when, if you get to that list, would you kind of want to be in the top 100? Do you kind of do a few bad things just to try and nudge it up? Because, you know, you've been... Well, this sounds like, right? You don't want to be 104. No, you want to be 99 or top 10, maybe.
Yeah. Well, he used to be in the top 10, but he hasn't done anything that bad to America for about 15 years.
Okay, I see what's happening here. Comeback. This is the comeback.
As I understand it, he runs some great big criminal operation, mafia style, which cost obviously a lot of people money, caused lots of crimes. He's now in Russia. He's way out of reach of the American authorities. And he's dripped. He's sort of plopped down the list. He's no longer causing that. Anyway, that appears to be who this cyber crime group have named themselves after. There's no reason to believe that it's actually connected with him. But they posted a message on their website, on the dark net, claiming that they had hacked Epic Games. Because, of course, that's what these gangs do these days, these ransomware gangs. They advertise who their latest clients are. In other words, the companies they've hacked, how much data they've taken. Quite often, they talk about their market capital as well, as to how much money these organizations have. And the newspapers all talked about Epic Games have been hacked. This hacking group have said it. But some people actually went to the effort of asking Epic Games and said, so you've been hacked then? And Epic Games said, not as far as we know. What? We're investigating. I can understand this because it's not always easy to know if you have been hacked or not. Because when it's something digital which has been taken, when it's something that's been copied as opposed to something that's been physically stolen, it's not the Mona Lisa has left a gap on the wall. Right. Then it's hard to know if it's happened. And in a particular case of Mogilevich, they weren't presenting any evidence that the hack had happened. So Epic Games said, there's currently zero evidence that these claims are legitimate. We haven't been contacted by this gang. They haven't provided any proof of this. All we can see is a screenshot, which has been posted up on Twitter, of their web page on the dark web saying that they've hacked us.
I find it super weird. I'm not surprised that some people would go report this early, right, based on their name. But are you saying that there was reputable press that were talking about this?
Yes, all kinds of press. I was contacted by some security vendors, PR agencies as well, saying, oh, here's our comment on the Epic Games hack in the aftermath of this. So you've got to be careful. And what Mogilevich did was they said, well, look, if you want proof, you are going to have to hand over $15,000 because we don't want, they said, we don't want to hand over any evidence which could be used by other people to claim that they've hacked Epic Games.
So they want a down payment. They want a deposit.
Right. Yeah. It's if you want the evidence, give us $15,000, then we'll give you the proof.
This is, I've not heard this before. Have you heard this before?
Not really, no. Normally they show you something, don't they? Yeah, they kind of show off. Even if they were adapted a bit or they would publish a bit.
There's been times where claims have been made and it's well, where's the evidence? And the evidence hasn't transpired. But it's interesting, Epic are being very transparent in their statement, aren't they? Saying, you know, we're investigating. They're not just saying we're investigating full stop. They're saying we have no evidence and they've given a bit of detail there. But this whole thing of give us 15,000 for us to give any proof, as far as I know, that's new.
So the gang are saying we're not going to produce any evidence of the hack because others might use this or claim to have conducted a similar hack. Epic Games are saying, well, we can see no evidence there's been a hack at all. And Epic Games isn't the first company which has allegedly been hacked by Mogilevich. They also claimed last month to hack a subsidiary of Nissan. They also claim to hack Ireland's Department of Foreign Affairs and another outfit called Bizarre Voice. But here's the thing. Here's the thing which has now emerged. A Mogilevich spokesperson. Now, okay, if you're dealing with a ransomware gang, what's the kind of name you expect of a criminal operation? What would the name be of one of their spokesmen? Nigel. Nigel Fingers McVitie, you know, Feathers McGraw. Or something that. Well, actually, it was Pongo. So Pongo has come up. And it appears that Mogilevich isn't what it was pretending to be. They've now said, we're not a real ransomware gang at all. They're saying, we are a professional group of scammers who pretend to hack big companies in order to trick people.
Yeah. Try and pin that on me. Try and pin that in your legal system, huh? Dancey, dance, dance, dance.
Well, they're still saying that this is a way to make money. So they say this. They say their scam involves multiple layers. They say it involves false claims where they pretend to hack major companies to gain attention. Okay. They claim that it's about fake ransomware access. So they offer to sell access to a non-existent ransomware infrastructure. So they claim to be ransomware as a service. So they're offering to take on board new affiliates. Jesus Christ. The world's going crazy. And if you sign up and give them money.
So they're scamming the ransomware affiliates amongst all of the other stuff they're doing. Wow. That's right. They're also, you remember, they're asking for $15,000. So it's like, you have to give us proof that you can pay $15,000, they're saying. Send us a screenshot of your cryptocurrency wallet so that we can see that you've got that much money in the cryptocurrency. What, $15,000? It's a dozen. Yeah, yeah.
Do you know what amazing yeah and you're never allowed anymore to say oh wow how is someone duped by that or by something because the world's gone mad. Look at the lengths.
The layers of things. Yes. And they have no shame. Yes. It goes to show just when we think we know what the criminals are doing, you know, pretty much. We know their operations. We know how they're working. Then something like this comes along, layers upon layers.
Someone called Pongo has outsmarted many other people. By the way, they claim that the most money they've made, they claim that they fabricated a data breach at the drone company, DJI. I don't know if you know that. They're quite a popular drone manufacturer. They claim they were able to scam someone for $85,000 after claiming that they'd hacked them. Now, can we trust them? No.
You'd have to ask that question. Everything that comes out of their mouth is just verbal blah, blah. Yeah.
They say we don't think of ourselves as hackers, but rather as criminal geniuses. Well, I'm not sure about that. Thanks for that. Noted.
I'm not sure anyone who ever calls themselves a genius is actually a genius. If you're calling yourself that.
Yeah. But these companies who they say have been hacked are suffering. Obviously, they have damage done to their reputation. They're going to incur expenses investigating the false claims, having to get their PR companies or legal department involved. And in some cases, we've even seen lawyers rush to file class actions, go in for compensation for a data breach, which has never actually happened, purely because someone called Pongo has claimed that it has.
Wow. And the stress of this, right? When you're working for an organization and there is this apparent data breach, the stress that causes everybody directly and indirectly in that organization can be huge. And then to turn it around and find it's actually just a scam within a scam. I just think there's
A weird line, though, that's been grayed out because I can see people banding this around on socials going, oh, my God, did you hear about this? And if you're a good journalist you'll be oh that's interesting let me do some digging.
Right yeah but everyone now is racing to be the first out with the news. I don't care
If you're calling yourself a newspaper and you're saying trust us not social media
Yeah but also there have been hacked companies who've kept quiet about hacks for a long time or said we haven't seen the evidence and then later you know a month and a half later have to admit, well, oh yes, there was something which happened.
It can be very hard, can't it, to make sense of it in the early days? And that's what this group is relying on, right? They're relying on how difficult it can be to see the wood from the trees. Maybe everyone should just slow the
Down. Maybe that's what has to happen, right? Everyone just has to chill out, take their time, and think about things before they run around.
As far as we know, there's no actual proof that Pongo and the Moglovich gang has actually ever scammed anyone for any money at all. But they have done, they've got journalists to write about them, helping make them famous. And indeed, podcasters talk about them.
I'm just imagining a bunch of these guys, right? Sitting around, you know, smoking a big doobie and going, you know what we could do? Do you know what we could do? And then coming up with this insane plan and then somehow they were able to pull it off in the real world. And what does that say?
Yeah. I think if the doobie were that big, they would never, they would have come up with the idea, but maybe not actually imagined it. Jess, what have you got for us this week?
Well, I am continuing the theme of your last few episodes and unfortunately, because we've been talking about ransomware for a while, continuing the theme of lots of conversations in cybersecurity talking about, you've guessed it, ransomware. A ransomware attack that has reportedly affected over 67,000 pharmacies and maybe around 130 million customers in the US. It seems that the Black Cat AlphV Group are back with an attack on Change Healthcare. I had not heard of Change Healthcare until last week. Hearing a lot about them now. They connect US healthcare providers with the insurance companies who pay for their services and determine what patients owe. So in the US, when you're going to get your prescription, often it's a co-pay thing. I'm still learning the system here, but co-pay thing where insurance will pay most of it and you as the patient might pay a small sum.
You go into Walgreens or CVS or somewhere like that, you don't have to pay the full charge because some of it's been paid by your insurance. Exactly. And you've been already paying your insurance and that's what it's there for, right? So you're living out in the States now, Jess. Do you know anyone who's been affected by this? I have heard from a few people. I don't know anyone directly, but heard from a few people and certainly been reading a lot about it. Which is when you've run out of the medicine. Right, exactly. That's when you need it the most, isn't it?
When you need it. And suddenly you're confronted with this. You haven't been told in advance, no preparation, and you stood there in a pharmacy. You're probably feeling pretty vulnerable.
So basically, the insurance companies are refusing to pay out on good faith at the moment is basically what's happening.
I think it's Change Healthcare. They're the bit which actually look it up on your insurance records and can tell the pharmacist, yes, this is being paid for by so-and-so. Therefore, they don't have to pay so much. Yeah. So that bit of the infrastructure isn't working. Supply chain meltdown. Yeah. It is. And the pharmacies are then stuck.
And they don't have a ton of cash there. Often independent places. I know there's some big ones, but I'm sure that maybe independent ones also got hit. Yeah, yeah. It's affecting so many, said to be costing hospitals in the US millions.
A bigger attack than that done by the politicians over the years. That's really bad then, isn't it, health care system?
I mean it does open up a whole debate doesn't it of people paying for health care and the kind of impact that it can have when you don't have insurance covering your payments for whatever reason that may be if it's ransomware or something else. And so it's had this huge impact, it's really hit the headlines, there's been lots of people talking on social media, of course, about the impact that it's having on them personally. And just as we were going to record, I saw Wired reporting that Black Cat have apparently received a payment of 350 Bitcoin, equivalent to about $22 million. So, of course, speculation that because of all of this disruption, they have been paid off. As we know, it can be a case where ransomware gangs are paid and then there's still a whole heap of disruption and it doesn't mean things necessarily just ping back to normal. And the news just in as we're seeing a return of the debate about whether to ban ransomware payments. So very interesting.
Yeah, we had that debate a few weeks ago on the show with someone and yeah it's a really difficult one isn't it?
I guess Change Healthcare probably has insurance for this kind of thing. So it's good that they were able to look up or their insurers were able to look up whether they were actually insured in order to pay the ransomware gang. At least that bit of the infrastructure was working.
And we know many ransomware gangs have said that they specifically target insurance companies to find out who's got insurance and then go after the people who've got insurance because they know. I think one of them described such targets as the tastiest morsel. I read that while writing my forthcoming book, Hacked, The Secrets Behind Cyber Attacks, where I talk about ransomware. Oh, it's not—
An upcoming book, Jessica. What?
What? This is hot news. Oh, did I mention that? You kept that quiet. Yeah, book coming out in April. And one of the chapters, of course, is on ransomware, as well as lots of other issues that we're dealing with in cybersecurity and some of these stories that emerge, some of these issues that come out and the impact they have on people.
Oh, I look forward to hearing more about your book in the pick of the week section later on. Carole, what have you got for us this week?
Okay, I'll kick off with a question. Have either of you been to some sort of therapy in your lives? Like, don't worry, I'm not going to ask for any details.
I thought you were volunteering to be my new therapist. I have.
I have therapy after every podcast.
Oh, do you? But one of the big challenges, well, at least for me, the start is how do you trust an absolute stranger with your deepest, darkest stuff? Yeah, now, if the fit's right between you and your therapist, I guess the trust grows and then you start sharing the hardest stuff in the name of improved mental health. So to that we say yay. But what happens if the trust between patient and therapist is broken? And you've already shared some stuff, like it could be absolutely catastrophic.
If you find out your therapist has got a bit of a big mouth, and they're gabbing off to other people about your private—
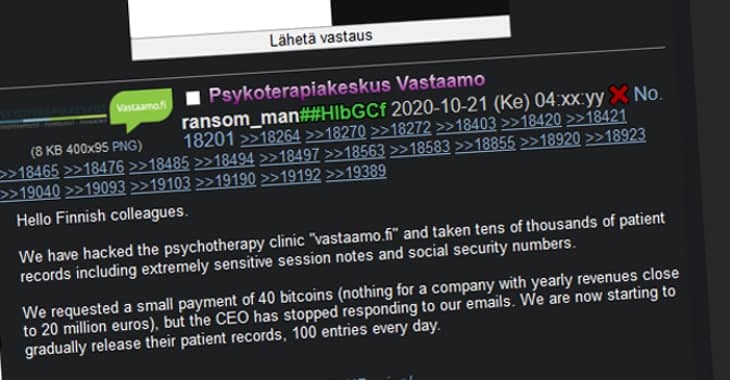
Yeah, or they're recording you secretly so that they can then share it. That would be horrendous. Okay, so this story starts way back in 2008. And there's this brand new psychotherapy clinic that was opened in Helsinki, Finland, called Vastaamo. And Vastaamo provided private mental health services to its patients through 25 therapy centers dotted across Finland. And they even subcontracted their services to the Finnish health system. And you would think, right, or maybe I'm crazy, but you would think, especially if you worked with the national health system, that you'd have pretty robust security in place. I mean, you know, therapists literally the protectors of secrets. You'd hope so. Well, we're wrong. So in October 2020, okay, so this is what, 12 years after they opened, Vastaamo announced to the world that they had been hacked. And worse than that, they said that the attackers had stolen patient records. Approximately 36,000 confidential psychotherapy patient records and 400 employee records were now in the wrong hands. And surprise, surprise, like we have a trifecta of ransomware discussion today. A ransom was demanded of approximately 450,000 euros in Bitcoin, and the threat was pay up or these records will find themselves in the public arena.
And this wasn't Pongo who had got in touch with Vastaamo, was it?
No, I don't think so.
No, I don't think it was.
No, no, no, no. But like, this is a tricky one, similar to yours, I think, Jess, which was pretty tricky. That question, to pay or not to pay? Because you're affecting here, you know, mental health. And I would like to think, right, that patient records are at least pseudo-anonymized. That's the GDPR word, isn't it? Like, so if I were a patient, maybe I would be recorded in my notes only via reference number. Just in case the information maybe got in the wrong hands, so they might know personal information, but they wouldn't be able to directly tie it to me specifically. And why not have a system like that? What's the harm of a system like that? Sounds sensible. Exactly. And since GDPR regulations have been passed, you know, this is 2020 we're talking about. This is not a crazy assumption on my part. But it turns out I am bonkers, guys. I'm totally bonkers. Graham, you're always right. The leaked patient database contained clients' personal information, such as their full names, home address, email address, social security numbers, name of the clinics where they receive treatments, therapists and doctor's notes from each session. So like things like I hate my boss, dad, mother, sibling, spouse. I have addictions to food, drugs, gambling, alcohol. I was mistreated, unloved, unseen, all that stuff. And all this found its way into the hands of the baddies, threatening to release the fully identifiable patient records to a zealous online crowd of nosy parkers.
Oh, absolute nightmare scenario for everyone. So the company—
Resists the ransom. They say, no, we're not going to pay. So the hacker, aka Ransom Man, clever. I see what he did there. He published the therapist notes of at least 300 patients, including politicians and police officers. And this was all on tour. But the hacker didn't stop there. He also thought it might be fun to approach victims directly because God, he had all their information, full name, email address, social insurance number. And why not email them directly with extortion demands, saying, hey, pay me 200 euros in Bitcoin within 24 hours, or actually the ransom will go up after that to 500 euros.
This is awful. He's just a shit, isn't he?
He's such a shit, whoever this guy is, but we're going to find out hopefully by the end of this story. Now, Graham, you talked about this on an earlier Smashing Security episode. But suddenly there was a huge leak, a 10 gigabyte data file containing the private notes of at least 2,000 patients and their therapists, right? All this appears on the dark web. But along with that, the attacker also managed to upload the contents of his very own computer at the same time. Basically advertising his involvement in the crime to anyone who might have been looking for him. And trust me, the Finnish authorities were.
We've all done it. We've all done the click, drag, drop oops, haven't we? Where we just copy far too much or attach the wrong file.
I once replied all. This is when I was working in a company and I replied all a message that I should not have replied all to. And boy, did I still had an Ethernet cable. Thank God I ripped that cable out so fast.
It's nice to know the criminals do this, too. You know, these criminal geniuses. Nice to know they make the same mistakes.
Well, unfortunately, with his mistake, he leaked basically his entire data dump of all these people who had all their secret notes with their therapist, all their information. Now, this accident of his led to the arrest, his arrest by French authorities, who soon extradited him to Helsinki. And as I speak, Ransom Man is now on trial and the prosecutors are asking for the maximum penalty of eight years. And he stands accused of aggravated computer break-in on nearly 10,000 counts of dissemination of information violating personal privacy and more than 20,000 counts of attempted aggravated extortion and 20 counts of aggravated extortion. So they've got him. He's got a lot of counts.
Because this was a huge crime in Finland, wasn't it? It was one of the biggest cases ever, I think, in terms of the number of people who were impacted.
And in terms of well-being and the psychological impact of this, you dread to think. To be an individual and receive an email like that, trying to extort money from you, otherwise your deepest, darkest fears and secrets are going to go out there in public, it's just a horrible scenario to think about, putting someone through that.
Okay, this is my big question for you two here. The moral quandary I got myself into when I was writing this. So this for me is invasion of privacy as serious as it gets. I think we all can agree on that. It's even led to suicides. And then I started wondering whether this hack is worse than the hack on adult hookup site Ashley Madison, which happened what, eight years ago? Where victims were effectively ousted online as cheaters. I think it's worse. Why?
Because people who are going to therapy are people who are already struggling with their mental health, whereas people who are having affairs with a virtual bot on Ashley Madison.
I would argue they probably are doing the same.
But I think they're probably less able to cope with the stress and anxiety. It's like they're going through a tough time anyway, which is why they're getting therapy. The last you want is the threat that your information is going to be made public.
And actually people can actually mandate you to go to therapy, right? That can be a court mandate or it can be a job mandate. So you may not even have chosen to go there on your own. And then you've opened everything up.
And any positive benefit that has come from that therapy could be in jeopardy from going through this, right? And then what? How are you going to recover from something like this? It has such an impact on trust doesn't it that it's I think it's worse. I mean it certainly reminded me of Ashley Madison as you were talking through it in terms of the impact. It just doesn't bear to think about doing this to people.
I don't normally say I hope he gets the whole maximum penalty because I'm not big on that but in this case it's pretty shitty. And there's also the fact that he went after individual patients, right? Proving that he knew everything and tried to extort. It's just, it's too gross for words.
That's a whole other level, isn't it? To do that and know that you are going directly to a person and presumably he dipped into the files and he read what was in those notes. And then to go to that person just is really hard to get your head around someone doing that.
The guy who's in court at the moment, Alex Kivimaki, I think his name is. Kivimaki, yeah. He's also been associated with Lizard Squad, if you remember them. They brought down PlayStation Network. Oh, yes. There's all kinds of other hacks and generally shitty behaviour, which has been coming from that corner of cyberspace. Graham, should we award him the Smashing Security Dipshit Award? Yes, dipshit of the year. I don't know, decade? I just think it's really, really scummy.
Well, I'll start with the week. We can maybe do it every week.
Oh, well, we could have a little jingle, maybe. Legacy managed file transfer tools are dated. They lack the security that today's remote workforce demands. Companies that continue relying on outdated technology put their sensitive data at risk. Well, this podcast is sponsored by Kiteworks, who enable organisations to effectively manage risk in every send, share, receive and save of sensitive content. To do that, they've created a platform that delivers content governance, compliance and protection to customers, tracking, controlling and securing sensitive content as it moves within, into and out of organisations, all while ensuring regulatory compliance on all sensitive content communications. Kiteworks provides the industry's first private content network for protecting risky third-party communications with secure email, secure file sharing, secure mobile, secure web forms, managed file transfer and governed SFTP servers. Visit kiteworks.com to get started today. That's kiteworks.com and thanks to them for supporting the show.
Smashing Security is also sponsored by Vanta. Managing the requirements for modern security programs is increasingly challenging and time consuming. Enter Vanta. Vanta gives you one place to centralize and scale your security program quickly, access risk, streamline security reviews and automate compliance for ISO 27001, SOC 2, and more. You can leverage Vanta's market-leading trust management platform to unify risk management and secure the trust of your customers. Plus, use Vanta AI to save time when completing security questionnaires. Smashing Security listeners, you get 20% off Vanta. All you lucky sausages have to do is visit vanta.com slash smashing to claim your discount. That's V as in Victor, A-N-T-A dot com slash smashing. And thanks to Vanta for sponsoring the show.
You've probably heard us talk about Collide before, but did you know Collide was just acquired by 1Password? Well, that's pretty big news since these two companies are leading the industry in creating security solutions that put users first. For over a year, Collide Device Trust has helped companies with Okta ensure that only known and secure devices can access their data. And that's what they're still doing, but now as part of 1Password. So if you've got Okta and you've been meaning to check out Collide, now's a great time. Collide comes with a library of pre-built device posture checks, and you can write your own custom checks for just about anything you can think of. Plus, you can use Collide on devices without MDM, like your Linux fleet, contractor devices, and every BYOD phone and laptop in your company. Now that Collide is part of 1Password, it's only going to get better. Check it out at collide.com slash smashing to learn more and watch the demo today. That's K-O-L-I-D-E dot com slash smashing, and thanks to them for supporting the show. And welcome back, and you join us at our favorite part of the show, the part of the show that we like to call Pick of the Week. Pick of the Week, Pick of the Week, Pick of the Week is the part of the show where everyone chooses to say it can be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website or an app, whatever they like. It doesn't have to be security related necessarily. Better not be. Well, my pick of the week this week is possibly slightly security related because we've just had this wonderful thing, what a fantastic thing that we have. We've had decimalisation, so we no longer use pound, shilling and pence. We went metric, right? We went decimal. Fantastic. That's happened. Many countries now, they've dropped the mile. They're using kilometres instead. Tremendous. But we still have this oddity, which is known as time, where we're splitting days up into 60-minute hours, and there's 24 hours of those in a day and there's 365 days in a year, not this year though because this year was a leap year. So every four years as we know we inject an extra day into the calendar and what do you know, things go wrong because yes ladies and gentlemen, even in 2024, 24 years after the millennium time bomb, software developers are still falling over themselves and have bugs in their code. In New Zealand, as we hit February the 29th, and of course New Zealand gets hit first because that's the first sort of major populated place where the new year comes in or where a leap year comes in, some of their gas stations across the country stopped people to pay for their gas, for their petrol on Thursday, because it couldn't cope with the date of February 29th. And so they weren't able to process payments, which I think is rather quaint in 2024, that that kind of thing is still happening, almost a quarter of a century after Y2K. And I also noticed that some security vendors and software vendors also failed as a consequence of the leap year bug. Including, yes, including a company known as Sophos. I don't know if you've ever heard of them.
No.
A number of their pieces of software failed on February the 29th, as did Citrix as well. Some of its software. Quel dommage.
Indeed, indeed.
And, OK, so here's my question. Is this a pick of the week or is this a nitpick of the week? Is my nitpick that leap years actually exist and we haven't yet decimalised time? Or is my pick of the week that I'm actually tickled by the fact that we're still having these problems? And let's not even talk about the Linux time bomb, which is, is it 2038? Let's not. I'm giving you warning now. I mentioned it here first. That's when we're going to have trouble as well with Linux. But, yeah.
Well, I like your nitpick pick of the week, Graham. And, you know, if we can do away with time, that means we can do away with time zones. And that would make me very happy.
And aging.
Right. Yeah, yeah. I'm on board. Fantastic.
Jess, what's your pick of the week?
Well, mine is not security related at all. I recently discovered the delightful Resident Alien when it landed, pun intended, fully on Netflix. Have either of you seen Resident Alien?
No, I haven't heard of it. What's it about? Well, it's been out there for a while, but it's only recently come to Netflix. We really enjoyed it. It is surprisingly wholesome and at times very much laugh out loud. It's kind of like a light sci-fi comedy about an alien who crashes on Earth during a mission to wipe us humans out of existence. So, you know, kind of premise we've heard before and doesn't necessarily sound necessarily hilarious, but I would highly recommend it. Not porn aliens, thank God.
No, certainly not up to season two anyway. I can't speak beyond that. It might all take a turn. But I loved Mork and Mindy when I was growing up and it's slightly, it's got a slight Mork and Mindy, but for 2024 vibe, slight undertone, you know of darkness but very funny and kind of wholesome. So if you're looking for some escapism that might also surprise you, check out Resident Alien, let me know what you think.
Fantastic. Thank you very much, Jess. Carole, what's your pick of the week?
Well, mine is a bit adult, surprise surprise, because I really enjoy house porn. Excuse me. You know, if I have a few hours to myself, I might choose to dim the lights, put on my joggers, get a cup of tea and open up Rightmove.
Oh, I see. Oh, right.
We really wondered where that was going. And then I might put in a random location. My most recent one was Cardiff, and then I put in some random price bracket and then I just gawk at people's houses.
Ooh, look at the extension on that one. That kind of thing.
Yeah, or you know, the current owner's a hoarder. Or once I saw open bills with addresses on the desk and I gave the story to BBC journalist Zoe Klein to warn people not to do that, to be more careful. Yikes, yeah. So this Reddit community, this is all on Reddit. This is actually a pic of the week that comes from fan of the show, CEO of Traced, Ben Jones. It's a Reddit sub called Spotted on Rightmove. And it's a community that collates wacky properties found on the UK house flipping site Rightmove. I don't know if you have it outside the UK. But you'll see hugely inflated house prices or incredibly nasty bathroom suites or there's one where it's, is that blood on the mirror? Or just unusually beautiful or nasty places to live. So one that I saw had this bath, you know, and people talk about the avocado suite being pretty hideous. This one is basically raspberry ripple ice cream. So it kind of looks like there's blood everywhere across the bath. There's another living room covered with swords of all sorts. And my favorite and the title in the subreddit, the title of the thread is this property is perfect if you want to warm up your lunch while taking a poop. Because the toilet is literally a foot away from the counter in the kitchen. That's not allowed, surely.
Is that in London and does it cost a fortune?
That would be my assumption. Yeah, most of them seem to be in London and costing an absolute fortune. So there you go. The Reddit sub that is my pick of the week is called Spotted on Rightmove. Have fun if this sounds like your thing and thank you Ben for this pick of the week.
Crikey, it looks quite addictive this. I mean there are a lot of people who love to look around other people's houses but these ones are, this is a curated list.
I just wish I'd known about it before and was more active use of Reddit because I have seen some absolute howlers and I think I could have just got a lot of social juice there.
Well, that just about wraps up the show for this week. Jess, I'm sure lots of our listeners would love to follow you online and find out what you are up to. What's the best way for folks to do that?
You can find me on pretty much all of the socials, including my recent foray into YouTube and TikTok at Dr. Jessica Barker. And shameless plug, of course, I have a new book coming soon, which you can pre-order now. Hacked, the secrets behind cyber attacks.
Brilliant. Super duper. And you can follow us on Twitter at Smash Insecurity. No G, Twitter wouldn't allow us to do that. We've also got a Mastodon account. And don't forget to ensure you never miss another episode. Follow Smash Insecurity in your favourite podcast app, such as Apple Podcasts, Spotify and Overcast. And huge, huge thank yous to our episode sponsors, Collide, Kiteworks and Vanta. And of course, to our wonderful Patreon community.
Until next time, cheerio. Bye-bye.
Who'd make a sandwich and have a shit? Who does that? That picture. Here, I was trying to get you this bathtub because it is just unbelievable.
Oh, that bath. Oh, my giddy aunt.
What would possess someone to ever? Oh, boy. Just honestly. The Raspberry Ripple is back on.
It looks like someone died in there. I think I saw something like this on Breaking Bad. Boy, oh boy.
Yeah. That's a whole other level. The Lucy matches, doesn't it? The Lucy and the Sink match. Oh, yes. And the Sink. Someone has committed to their vision. It's not turned out the way most of us might like, but someone's really gone all in on that. Brilliant. Jess, thank you so, so much.
Yes, thanks, Jess. Thank you. It was really nice, really good fun. And thank you so much for talking to us. We're very honoured, milady.
Hosts:
Graham Cluley:
Carole Theriault:
Guest:
Jessica Barker – @drjessicabarker
Episode links:
- Mogilevich claims it has breached Epic Games – Twitter.
- Fraudster’s fake data breach claims should remind media to be carefu what we report – DataBreaches.net.
- Prescription orders delayed as US pharmacies grapple with “nation-state” cyber attack – Bitdefender.
- US pharmacy outage triggered by ‘Blackcat’ ransomware at UnitedHealth unit, sources say – Reuters.
- Hackers Behind the Change Healthcare Ransomware Attack Just Received a $22 Million Payment – Wired.
- Vastaamo data breach – Wikipedia.
- The CEO who also ran IT, Strava strife, and TikTok tall tales – Smashing Security podcast.
- Ex-CEO of hacked therapy clinic sentenced for failing to protect patients’ session notes – Bitdefender.
- Ex-CEO of breached pyschotherapy clinic gets prison sentence for bad data security – Sophos.
- Vastaamo victims’ lawyer: Some took their own lives after patient record leak – Yle.
- Prosecutors call for maximum penalty over Vastaamo hacking – Helsinki Times.
- Self-pay gas station pumps break across NZ as software can’t handle Leap Day – Ars Technica.
- Citrix, Sophos software impacted by 2024 leap year bugs – Bleeping Computer.
- Resident Alien trailer – YouTube.
- Resident Alien – Netflix.
- r/SpottedonRightmove – Reddit.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Kiteworks – Step into the future of secure managed file transfer with Kiteworks.
- Vanta – Expand the scope of your security program with market-leading compliance automation… while saving time and money. Smashing Security listeners get 10% off!
- Kolide – Kolide ensures that if your device isn’t secure it can’t access your cloud apps. It’s Device Trust for Okta. Watch the demo today!
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a supporter via Patreon or Apple Podcasts for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky at @smashingsecurity.com, or on Mastodon, on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.